What Is a Zero-Day Exploit and Why Are They Dangerous?
The cybersecurity landscape has seen a significant escalation in threats over the past year. In the third quarter of 2024, organizations experienced an average of 1,876 cyberattacks per week, marking a 75% increase compared to the same period in 20231.
What is a zero-day exploit in cybersecurity? A zero-day attack happens when hackers exploit a software flaw before developers can patch it, leaving systems vulnerable. The scale of this threat is significant — Mandiant’s analysis of 138 actively exploited vulnerabilities disclosed in 2023 found that 97 (70%) were zero-day attacks2. This highlights how widespread and damaging these exploits can be.
In this guide, I’ll break down what zero-day exploits are, why they’re so dangerous, and, most importantly, how you can stay protected. Whether you’re worried about your personal data or managing a business that depends on secure systems, understanding these threats is essential. Let’s get started!
What Is a Zero-Day Exploit?
A zero-day exploit is a type of cyberattack that targets a vulnerability in software or hardware that the developer or vendor isn’t yet aware of. This means the flaw has not been patched or fixed, and attackers can take advantage of it without interference from safety precautions.
Once hackers discover the vulnerability, they can exploit it to gain unauthorized access, steal data, or disrupt systems, all before a solution is put in place. Since there is no fix, the system is wide open to attack. The term “zero-day” refers to the software creators having zero days to resolve the issue once it is revealed and used by attackers.
What Is the Difference Between a Zero-Day Exploit, Attack, and Vulnerability?
It’s important to understand the difference between these terms, as they are often used interchangeably but have distinct meanings:
- Zero-day vulnerability: This is a security gap that developers are unaware of and hackers can exploit.
- Zero-day exploit: This is the method or tool used by attackers to take advantage of the zero-day vulnerability. It’s the act of exploiting the flaw to compromise the system.
- Zero-day attack: This is the actual event in which the zero-day exploit is used to launch an attack, usually with malicious intent, such as stealing sensitive information, installing malware, or gaining unauthorized control over systems.
Zero-Day Exploit Stages
Zero-day exploits typically unfold in a series of crucial stages in the attack’s lifecycle. Understanding these stages can help highlight vulnerabilities and the timeline during which these exploits can cause harm:
- Discovery. The vulnerability is first identified by hackers, security researchers, or software developers. If uncovered by hackers, they often keep it hidden to exploit it later.
- Exploitation. Hackers use the vulnerability to craft an exploit, which allows them to gain unauthorized control of the target system.
- Weaponization. The exploit is packaged with additional malicious tools, such as malware or viruses, to make the attack more effective and stealthy.
- Delivery. The exploit is delivered to the target, allowing it to infiltrate the system.
- Post-exploitation. Once the exploit successfully compromises the system, hackers can steal data, install backdoors, or cause other damage, all without detection until the patch is released.
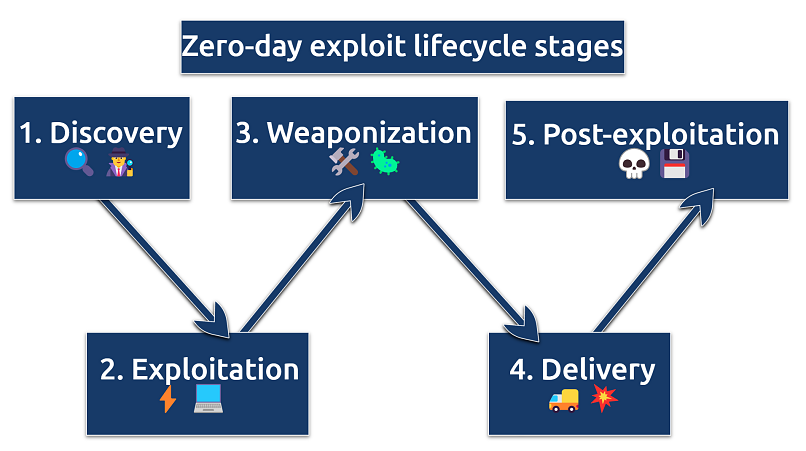 These stages highlight the rapid and stealthy nature of zero-day exploits
These stages highlight the rapid and stealthy nature of zero-day exploits
How Do Zero-Day Exploits Differ From Regular Cyberattacks?
While all cyberattacks aim to exploit weaknesses in systems, zero-day exploits stand apart from regular attacks in one significant way: timing. In a typical cyberattack, the vulnerability being exploited is already known to the software vendor, and patches or fixes are often available to address it. In these cases, the software is vulnerable because the patch has not been applied or users have not updated their systems.
On the other hand, zero-day exploits target unknown vulnerabilities. This gives attackers a significant advantage, as they can carry out the attack without the risk of detection or interference from existing safety measures. The lack of a patch means the system remains open to exploitation, often for some time, until the vulnerability is discovered and resolved. This makes zero-day exploits especially difficult to defend against in real-time.
Why Are Zero-Day Exploits Dangerous?
Zero-day exploits are particularly harmful because they give attackers an undetected window of opportunity. Attackers can exploit the flaw without facing immediate countermeasures, making zero-day exploits highly effective in infiltrating systems, often without triggering any alarms from existing security protocols. Hackers may use various methods to deliver the exploit, such as phishing emails or malicious downloads.
Additionally, the exploitation can continue for weeks or even months before a fix is made available, allowing hackers to access sensitive data, install malware, or cause significant damage. The speed and stealth with which these exploits can be used make them a formidable threat to both individuals and organizations.
One reason zero-day exploits are so dangerous is the sheer volume of potential vulnerabilities that attackers can exploit. For instance, Microsoft applications have reportedly contained about 0.5 defects per 1,000 lines of code in their released products3. With Windows 11 estimated to have around 60 million lines of code, this suggests that the operating system could harbor as many as 30,000 bugs — any of which could be used as an entry point by attackers.
Who Performs Zero-Day Exploits?
Zero-day exploits are typically carried out by various groups of cybercriminals, each with different motives. Cybercriminals are often driven by financial gain, targeting individuals and organizations to steal confidential data, access systems, or deploy ransomware. Hacktivists, motivated by political or social causes, may use zero-day exploits to make a statement or disrupt operations.
Corporate espionage actors, typically working for rival companies, may use these attacks to seek trade secrets or sensitive information. Additionally, state-sponsored hackers often engage in cyber warfare, targeting foreign governments or critical infrastructure to cause disruption.
How Zero-Day Attackers Find Vulnerabilities?
Hackers use several methods to identify zero-day vulnerabilities, including reverse engineering, vulnerability scanning, and leveraging insider information. Reverse engineering involves deconstructing software updates or patches to uncover weaknesses in the code.
Vulnerability scanning tools automate the process, searching for flaws the vendor has not yet discovered. In some cases, insiders with access to confidential data or software code may leak or sell vulnerabilities to external parties.
Targets of Zero-Day Exploits
Zero-day exploits can target almost any system or network, but certain ones are more likely to be targeted because of their higher value. Large corporations, especially those in finance, healthcare, and technology, are prime targets as they hold valuable intellectual property, financial data, or user information. Government agencies are also high-value targets for espionage or political gain.
Critical infrastructure systems, such as power grids, water supplies, or communication networks, are often targeted by nation-state actors to cause widespread disruption. Additionally, high-profile individuals, like executives or those with privileged access to sensitive systems, may also be targeted to gain unauthorized access, extort money, or even expose personal information through doxxing, a practice of publicly revealing private details as a form of harassment or coercion.
How to Detect Zero-Day Exploits?
Detecting zero-day exploits is tricky because the vulnerabilities they target are new and unknown to software vendors, leaving no pre-existing defenses in place. Traditional detection methods, like signature-based tools, work by spotting known patterns or “signatures” of malicious code. But with zero-day exploits, there’s no existing pattern to recognize, making these methods ineffective.
Instead, behavior-based detection focuses on monitoring activity within a network and flagging anything unusual. For example, it might detect suspicious behavior like unauthorized access attempts, abnormal data flows, or unexpected system activity. This approach helps organizations spot potential threats even when no clear signature exists.
To stay ahead, many organizations are turning to advanced tools like anomaly detection, machine learning algorithms, and vulnerability assessment tools. These technologies track system behavior over time, helping to identify anything out of the ordinary that could point to a zero-day exploit or highlight weaknesses before they’re exploited.
How to Protect Yourself Against Zero-Day Exploits?
Protecting against zero-day exploits requires a proactive and comprehensive approach. Here are the most important strategies for minimizing the risk of falling victim to these attacks:
- Keep software and OS updated: Regularly update software and operating systems to apply patches that fix known vulnerabilities, reducing exposure to zero-day exploits.
- Use antivirus software. A strong antivirus program with behavior-based detection can help block malware associated with these exploits.
- Stay cautious of phishing. Avoid clicking on suspicious links or attachments in emails and messages, as phishing is a common delivery method for zero-day exploits.
- Use a VPN. VPNs encrypt all online traffic, making it more difficult for attackers to intercept and exploit sensitive data.
 By hiding your real IP address, VPNs make it harder to target specific devices or networks
By hiding your real IP address, VPNs make it harder to target specific devices or networks
- Limit applications. Only use essential apps, as unnecessary or outdated software increases your vulnerability to attacks.
- Use a firewall. A firewall helps monitor and block suspicious traffic, offering an additional layer of protection against zero-day attacks.
- Stay informed. Routinely check for new vulnerabilities and security updates to ensure your systems are protected against emerging threats.
- Use network segmentation to protect your systems. Network segmentation helps contain zero-day exploits by dividing your network into isolated segments, preventing attackers from easily accessing critical systems. For instance, you can separate financial servers, customer databases, or IoT devices into distinct segments, ensuring that a breach in one area doesn’t spread to sensitive parts of the network. This approach adds an extra layer of protection by limiting the movement of threats within your system.
- Educate employees. To reduce human error, train staff to recognize phishing attempts, follow cybersecurity protocols, and safely handle classified data.
- Implement continuous monitoring. Use tools to detect potential weaknesses across all assets before they become exploitable, allowing you to address vulnerabilities proactively.
- Prioritize automated remediation. Automate the process of fixing vulnerabilities in real-time, significantly reducing the window of opportunity for attackers.
Examples of Zero-Day Exploits
Zero-day exploits continue to be a major concern for cybersecurity worldwide, with an increasing number of attacks and vulnerabilities discovered each year. Here are some of the most notable zero-day exploits that have made headlines in recent years:
- Chrome vulnerability. In 2024, Google patched its tenth zero-day vulnerability of the year in the Chrome browser4. This particular flaw, identified as CVE-2024-7965, resided in the V8 JavaScript engine and allowed attackers to execute arbitrary code via crafted HTML pages. Users were urged to update to version 128.0.6613.84/.85 to mitigate this risk.
- Mozilla Firefox zero-day. In October 2024, Mozilla addressed a critical zero-day vulnerability, CVE-2024-9680, in Firefox. This use-after-free bug in the Animation timeline component enabled attackers to execute arbitrary code5. The flaw was actively exploited in the wild, prompting users to update to Firefox version 131.0.2 or the corresponding Extended Support Release versions immediately.
- Barracuda Networks security breach. In 2023, a zero-day vulnerability in Barracuda Networks’ Email Security Gateway was exploited by state-sponsored hackers. This breach allowed attackers to bypass security protocols, compromising the email systems of numerous organizations worldwide6.
- Log4Shell. Discovered in December 2021, the Log4Shell vulnerability (CVE-2021-44228) in the Apache Log4j library permitted remote code execution. This flaw led to a global cybersecurity crisis, affecting countless organizations across various sectors7.
- Kaseya. In July 2021, attackers exploited a zero-day vulnerability in Kaseya’s VSA software, leading to a widespread ransomware attack. This incident impacted over 1,500 organizations globally, highlighting the risks associated with supply chain vulnerabilities8.
- Zoom zero-day. During the COVID-19 pandemic in 2020, a zero-day vulnerability in Zoom allowed attackers to gain unauthorized access to users’ systems through malicious links sent via the platform’s chat feature9.
- Apple iOS zero-day. In 2020, Apple patched critical zero-day vulnerabilities in iOS, one of which enabled attackers to remotely compromise iPhones. This exploit targeted core components of the operating system, granting remote control over affected devices10.
- Stuxnet. In 2010, one of the most famous zero-day attacks in history, Stuxnet targeted industrial control systems (ICS) in Iran, particularly its nuclear enrichment facility. This highly sophisticated malware exploited multiple zero-day vulnerabilities in Windows to disrupt operations and sabotage Iran’s nuclear program.
FAQs on Zero-Day Exploits
Can antivirus software protect against zero-day exploits?
Modern antivirus software has advanced significantly to better defend against zero-day exploits, unlike traditional programs that struggle with such unknown threats. However, combining antivirus tools with additional security measures is essential for stronger protection.
Today’s advanced solutions use behavior-based detection, machine learning, and heuristic analysis to spot unusual system activities that may signal a zero-day exploit. While these tools can’t guarantee complete protection, they significantly improve the ability to detect and respond to emerging threats, even if the exploit is still unknown.
How long does it take for a zero-day vulnerability to be discovered and patched?
The timeline for discovering and patching a zero-day vulnerability varies significantly and can range from days to years. Once a vulnerability is discovered, the time to develop and release a patch typically spans from a few days to several months, depending on the complexity of the flaw and the software vendor’s resources. However, it’s important to note that zero-day vulnerabilities may remain undetected and exploited for extended periods before discovery.
Are zero-day exploits only a risk for large organizations?
No, zero-day exploits aren’t just a risk for large organizations. Smaller businesses and individuals are also vulnerable, as any system with unpatched flaws can be targeted. Smaller companies may be especially at risk due to limited safety resources, while individuals can face exploitation through personal devices and online accounts.
What should I do if I think I’ve been affected by a zero-day attack?
If you think you’ve been affected by a zero-day attack, disconnect from the network immediately to prevent further damage. Then, run a full system scan with updated antivirus software to detect any malicious activity. If you’re part of an organization, notify your IT team or a cybersecurity professional.
Change any compromised passwords, report the breach if sensitive data was accessed, and stay updated on patches or fixes for the vulnerability. Taking steps to strengthen your security can also help prevent future incidents.
How does a zero-day vulnerability differ from malware?
A zero-day vulnerability is a security flaw in a system, while malware is the malicious software that exploits such flaws. A zero-day vulnerability serves as an entry point for attacks, but it is not harmful on its own. In contrast, malware is designed to damage, steal data, or take control of a system, often using zero-day vulnerabilities to infiltrate undetected.
What is the difference between a zero-day bug and a backdoor?
A zero-day bug is an undiscovered security flaw, while a backdoor is a hidden method for unauthorized access. A zero-day bug becomes dangerous when exploited before a fix is available, whereas a backdoor is often intentionally placed (or secretly inserted by attackers) to bypass standard authentication. While a zero-day exploit can be used to create a backdoor, the key difference is that one is a vulnerability, and the other is a deliberate access mechanism.
What is the difference between a zero-day attack and ransomware?
A zero-day attack exploits an unknown software vulnerability, while ransomware is malicious software that encrypts files and demands payment for their release. Zero-day attacks are often stealthy and can go undetected for long periods, allowing attackers to gather data or gain persistent access.
In contrast, ransomware attacks are immediate and obvious, as victims are quickly notified of the encryption and ransom demand. While both can cause significant damage, zero-day attacks are typically used for espionage, data theft, or long-term infiltration, whereas ransomware is primarily financially motivated.
Conclusion
Zero-day exploits are a serious cybersecurity threat, allowing attackers to take advantage of unknown vulnerabilities before a fix is available. These attacks can target anyone — from individual users to large organizations — making it essential to stay informed and take proactive security measures.
Keeping your software updated, using strong passwords, enabling multi-factor authentication, and being cautious with email attachments or unknown links can help reduce your risk. By staying vigilant and practicing good cybersecurity habits, you can better protect your data and devices from zero-day exploits and other online threats.
References
- https://blog.checkpoint.com/research/a-closer-look-at-q3-2024-75-surge-in-cyber-attacks-worldwide/?utm_source=chatgpt.com
- https://www.cybersecuritydive.com/news/zero-day-exploits-rise-mandiant/730265/#:~:text=Wednesday%20blog%20post.-,Of%20the%20138%20actively%20exploited%20vulnerabilities%20disclosed%20in%202023%20and,zero%2Ddays%2C%20researchers%20said.
- https://www.mayerdan.com/ruby/2012/11/11/bugs-per-line-of-code-ratio
- https://www.sangfor.com/blog/cybersecurity/google-chrome-vulnerability-marks-10th-zero-day-exploit
- https://www.bleepingcomputer.com/news/security/mozilla-fixes-firefox-zero-day-actively-exploited-in-attacks/
- https://www.barracuda.com/company/legal/esg-vulnerability
- https://salt.security/blog/the-log4shell-cve-2021-44228-vulnerability-what-it-is-how-it-works-and-how-to-protect-yourself
- https://www.kaseya.com/press-release/kaseya-responds-swiftly-to-sophisticated-cyberattack-mitigating-global-disruption-to-customers/
- https://www.forbes.com/sites/daveywinder/2020/07/10/zoom-confirms-zero-day-security-vulnerability-for-windows-7-users/
- https://www.welivesecurity.com/2020/11/06/apple-plugs-three-zero-day-holes-ios/
React to this headline: